SubImage shows risk context and actionable fixes, not just vulnerability counts.
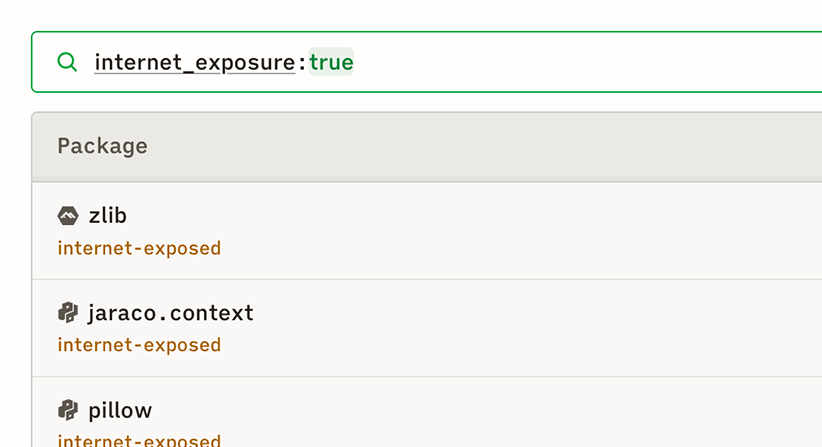
Is the vulnerable package in a running container? Is that container internet-exposed? Is there a path from it to sensitive data? If not, it drops in priority.
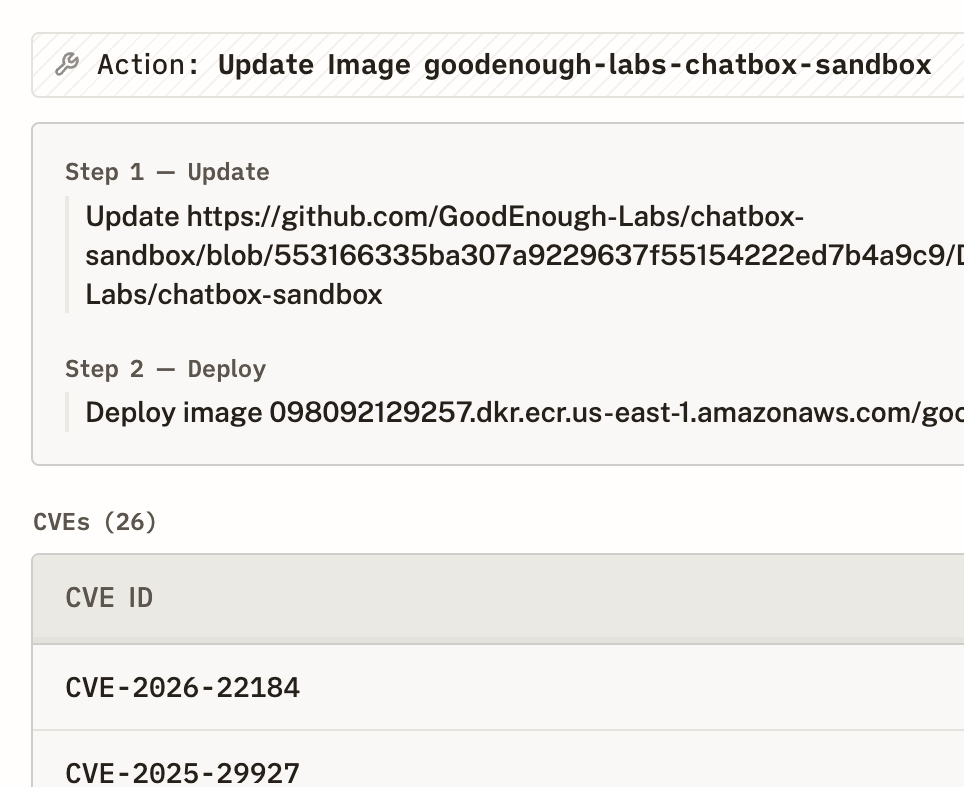
We show the fewest actions to fix the most risk. You see every container and image affected, whether the package is inherited from a base image, and the exact version that resolves it.
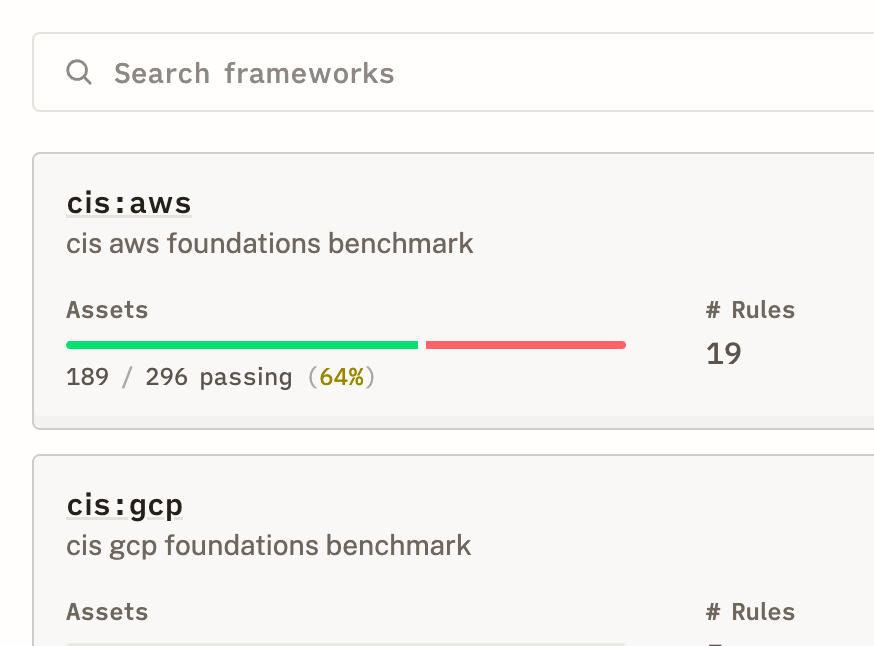
GRC teams get exportable compliance reports with risk breakdowns. Security engineers get the graph view showing which vulns sit on actual attack paths.
Known exploited vulnerabilities get flagged automatically so you never miss the ones actively being used in the wild.