SubImage runs cloud security posture checks and then tells you which failures actually sit on a dangerous path.
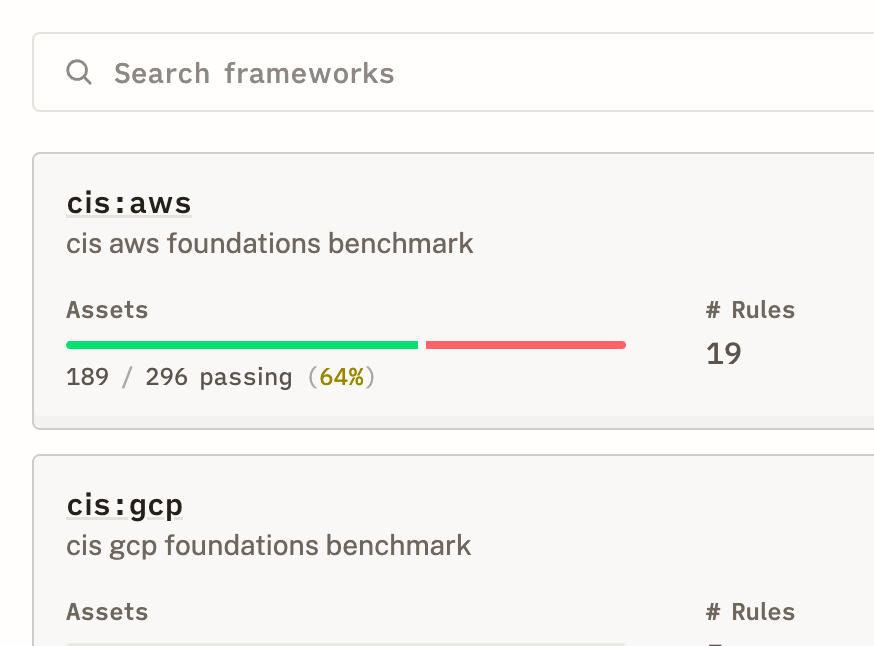
CIS Benchmarks, SOC2, NIST, PCI-DSS — the checkbox compliance your auditors need.
A misconfigured - but empty - security group on an isolated dev instance is not the same as one protecting your production API gateway. We know the difference because we map the relationships.
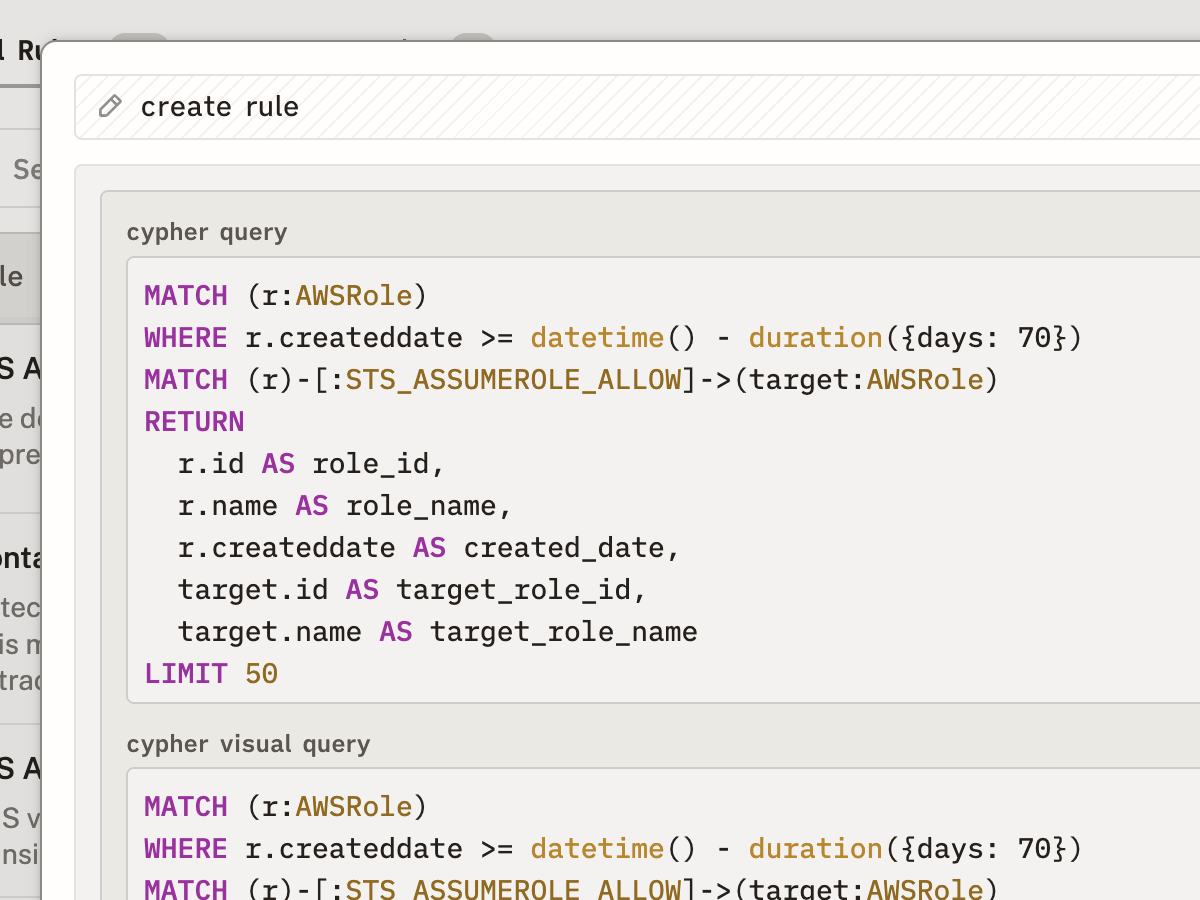
Your org has policies that don't fit CIS. Write them as graph queries: "Flag any IAM role that can assume into production AND was created in the last 7 days."
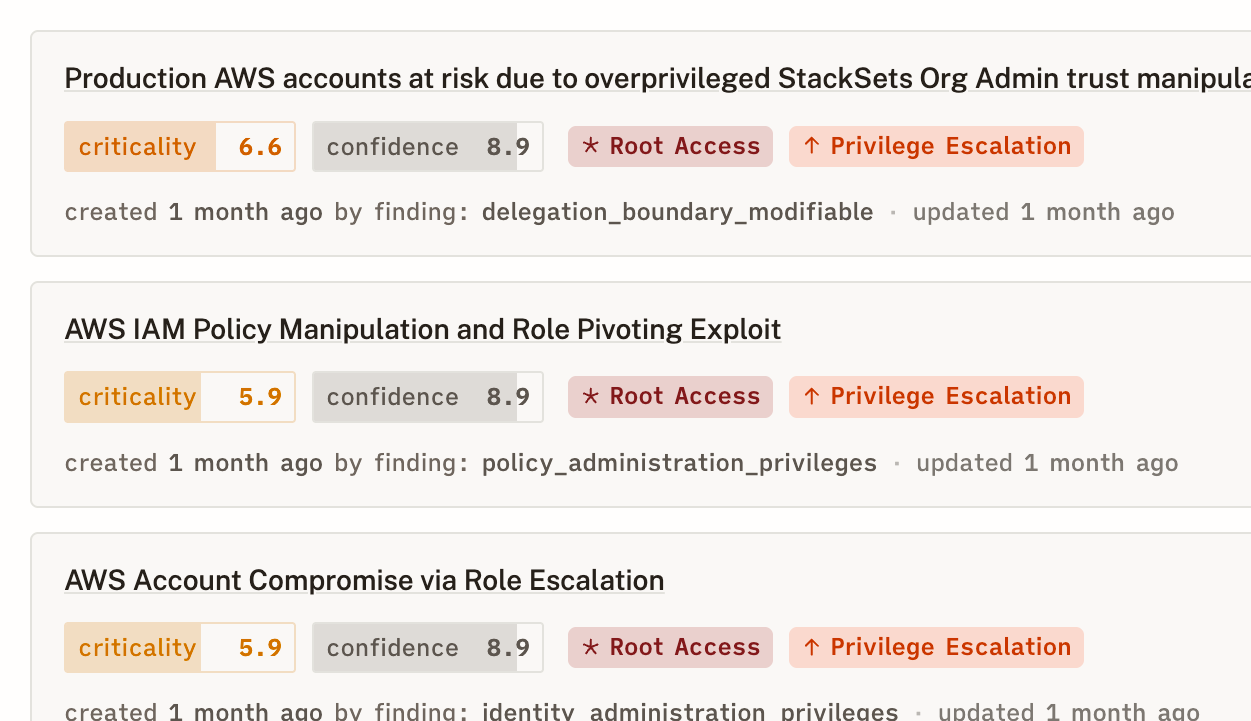
Every posture finding links to the attack paths it enables. Stop triaging in a vacuum.