We continuously map paths from internet-exposed entry points through lateral movement opportunities to your critical assets.
A HIGH or CRITICAL severity CVE in a container image may allow an attacker with network access to exploit the vulnerability and gain code execution inside the container.
Code executing inside an ECS container inherits the cloud permissions of any IAM role assigned by its task definition, including both task roles and execution roles.
An IAM role with s3:PutObject permission can upload or overwrite objects in a bucket, enabling data tampering or malware staging.
Model and trace any node's blast radius in response to potential compromise.
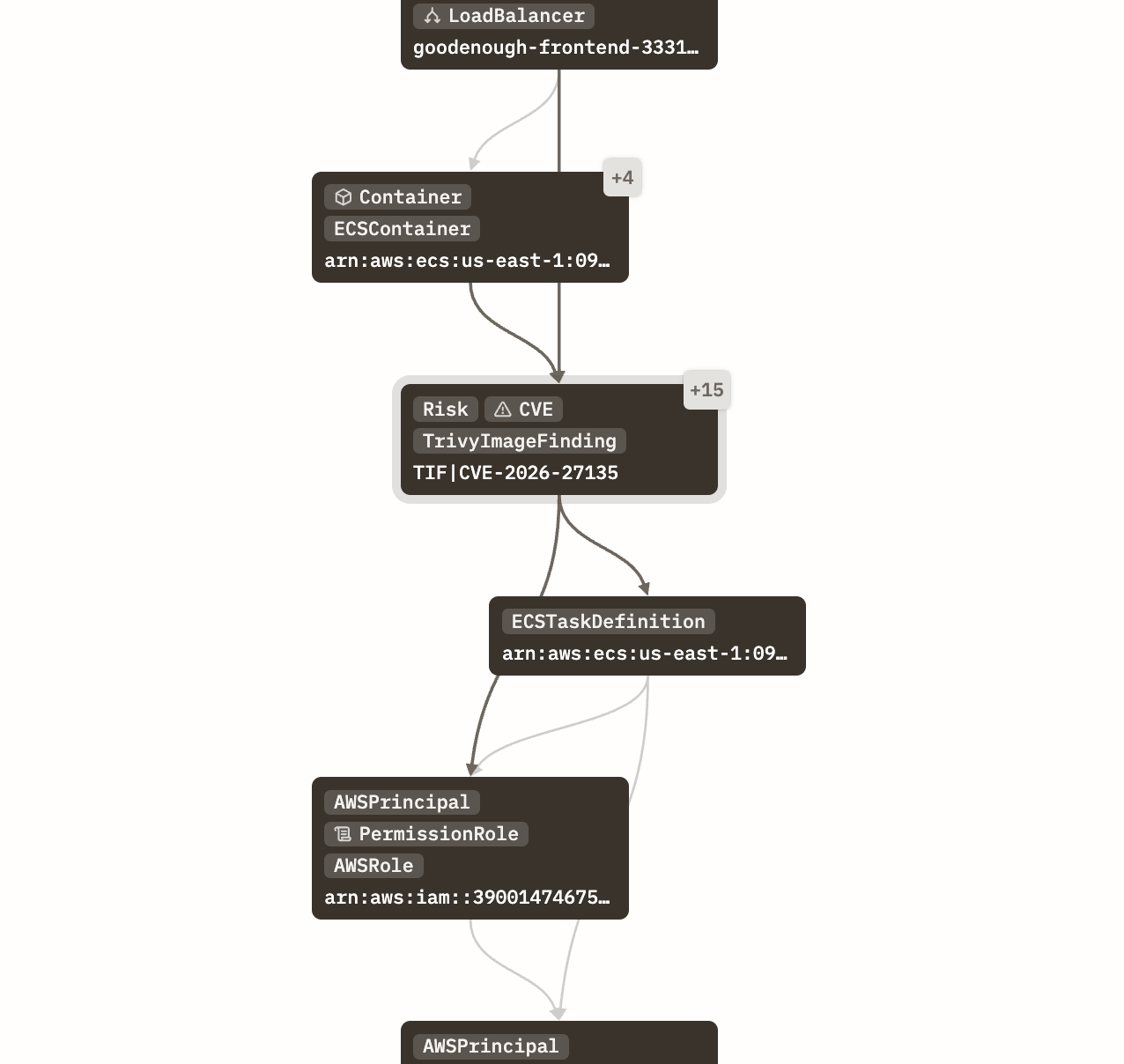
Each path shows you the cheapest fix — the single change that severs the path entirely. Fix one thing, eliminate an entire class of attack.
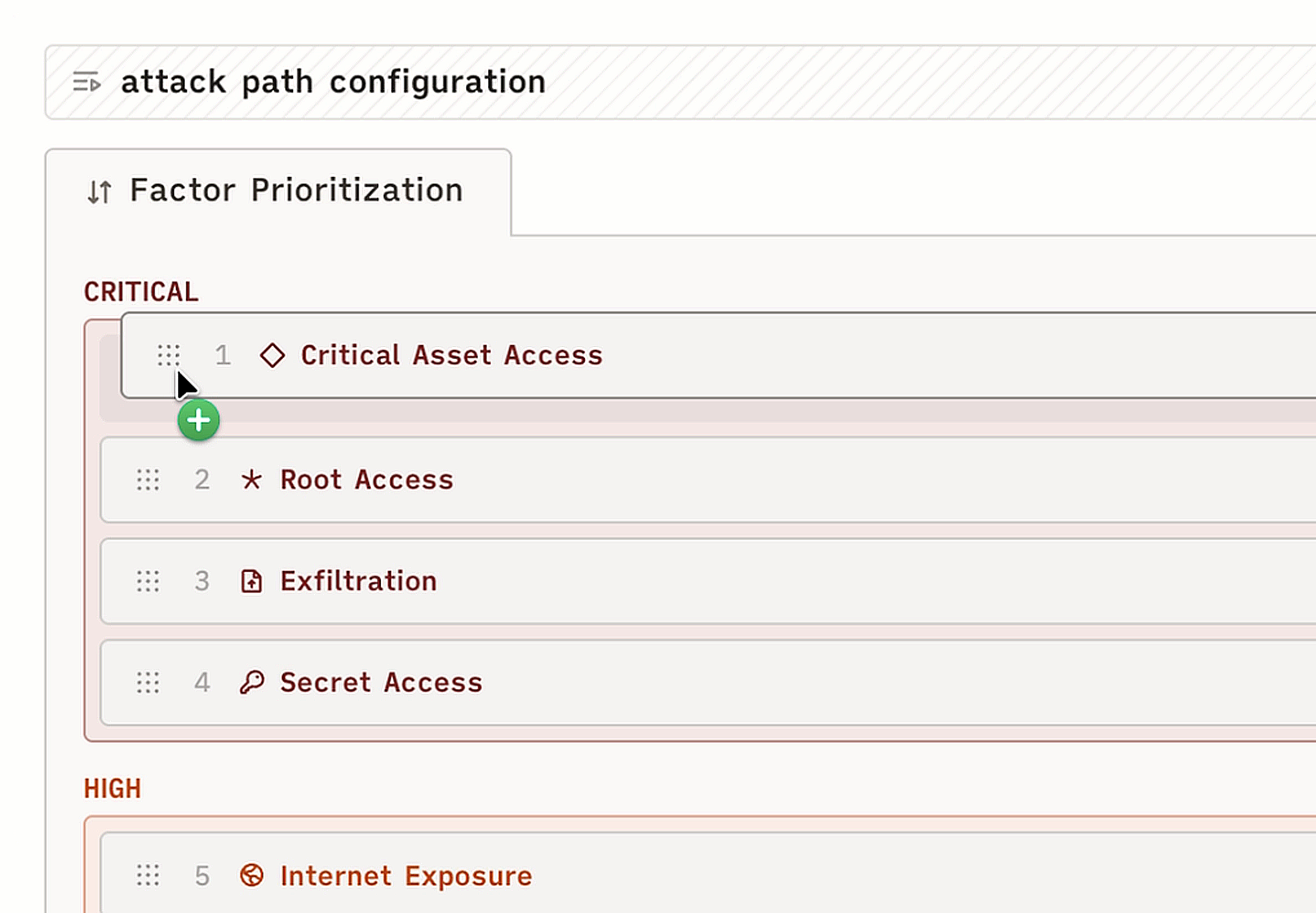
Tag your most critical assets — production databases, secrets managers, CI/CD pipelines — and we prioritize every path that reaches them.